111 | Add to Reading ListSource URL: www.bayswan.orgLanguage: English - Date: 2013-06-01 20:35:21
|
|---|
112 | Add to Reading ListSource URL: asthma.umich.edu- Date: 2008-09-11 00:00:00
|
|---|
113 | Add to Reading ListSource URL: www.securedbydesign.comLanguage: English - Date: 2014-02-25 02:33:07
|
|---|
114 | Add to Reading ListSource URL: gruss.ccLanguage: English - Date: 2016-05-12 04:58:22
|
|---|
115 | Add to Reading ListSource URL: people.cs.vt.eduLanguage: English - Date: 2017-06-19 09:45:20
|
|---|
116 | Add to Reading ListSource URL: www.sainteuphoria.comLanguage: English - Date: 2012-07-28 01:24:18
|
|---|
117 | Add to Reading ListSource URL: www.fire.ca.gov- Date: 2013-04-05 13:47:45
|
|---|
118 | Add to Reading ListSource URL: www.rennes.supelec.frLanguage: English - Date: 2009-10-01 09:50:26
|
|---|
119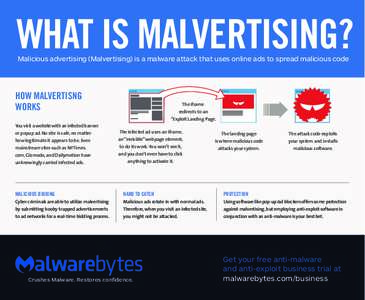 | Add to Reading ListSource URL: fr.malwarebytes.comLanguage: English - Date: 2016-05-10 22:50:01
|
|---|
120 | Add to Reading ListSource URL: www.ratsgymnasium-wolfsburg.deLanguage: German - Date: 2015-11-03 02:38:11
|
|---|