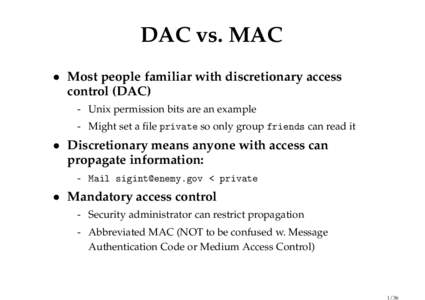
 Date: 2010-03-04 18:26:58Computer memory Bell–LaPadula model Covert channel Mandatory access control Classified information Htop CPU cache Access control Security clearance Security Computer security Computing | |  DAC vs. MAC • Most people familiar with discretionary access control (DAC) - Unix permission bits are an example - Might set a file private so only group friends can read it DAC vs. MAC • Most people familiar with discretionary access control (DAC) - Unix permission bits are an example - Might set a file private so only group friends can read it
Add to Reading ListSource URL: www.scs.stanford.eduDownload Document from Source Website File Size: 149,24 KBShare Document on Facebook
|
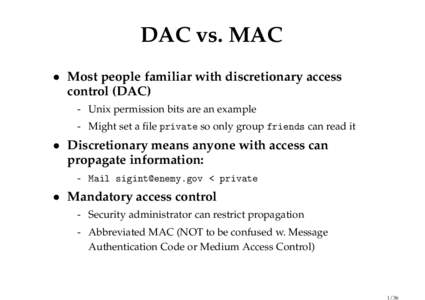




 DAC vs. MAC • Most people familiar with discretionary access control (DAC) - Unix permission bits are an example - Might set a file private so only group friends can read it
DAC vs. MAC • Most people familiar with discretionary access control (DAC) - Unix permission bits are an example - Might set a file private so only group friends can read it