41 | Add to Reading ListSource URL: mkorczynski.comLanguage: English - Date: 2015-02-15 17:10:50
|
|---|
42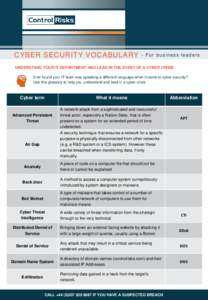 | Add to Reading ListSource URL: www.controlrisks.comLanguage: English - Date: 2016-08-04 06:27:46
|
|---|
43 | Add to Reading ListSource URL: static.usenix.orgLanguage: English - Date: 2011-08-24 13:54:47
|
|---|
44 | Add to Reading ListSource URL: www.cs.okstate.eduLanguage: English - Date: 2011-08-15 19:32:40
|
|---|
45 | Add to Reading ListSource URL: londonactionplan.orgLanguage: English - Date: 2016-04-26 15:59:23
|
|---|
46 | Add to Reading ListSource URL: www.wdin.orgLanguage: English - Date: 2011-09-23 12:49:50
|
|---|
47 | Add to Reading ListSource URL: www.cloudmark.comLanguage: English - Date: 2014-10-07 15:50:23
|
|---|
48 | Add to Reading ListSource URL: danlarremore.comLanguage: English - Date: 2012-12-18 10:08:00
|
|---|
49 | Add to Reading ListSource URL: norbert-pohlmann.comLanguage: English - Date: 2015-12-21 09:55:27
|
|---|
50 | Add to Reading ListSource URL: www.corero.comLanguage: English - Date: 2016-05-16 11:11:13
|
|---|