31 | Add to Reading ListSource URL: webfoot.comLanguage: English - Date: 2008-08-20 20:37:11
|
|---|
32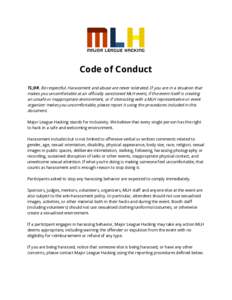 | Add to Reading ListSource URL: sachacks.ioLanguage: English - Date: 2018-10-25 23:07:17
|
|---|
33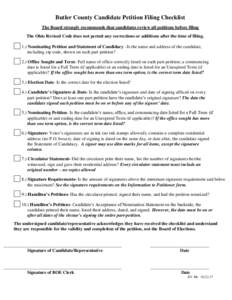 | Add to Reading ListSource URL: www.butlercountyelections.orgLanguage: English - Date: 2017-03-15 14:47:38
|
|---|
34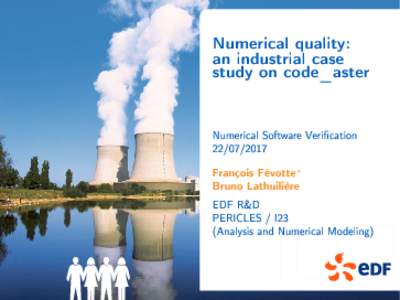 | Add to Reading ListSource URL: www.cs.ox.ac.ukLanguage: English - Date: 2017-07-27 09:38:49
|
|---|
35 | Add to Reading ListSource URL: hacken.ioLanguage: English - Date: 2017-10-12 11:58:38
|
|---|
36 | Add to Reading ListSource URL: zhang-sai.github.ioLanguage: English - Date: 2015-05-05 00:58:34
|
|---|
37 | Add to Reading ListSource URL: www.mfjenterprises.com- Date: 2018-09-06 12:41:54
|
|---|
38 | Add to Reading ListSource URL: www.butlercountyelections.orgLanguage: English - Date: 2017-12-05 11:09:38
|
|---|
39 | Add to Reading ListSource URL: uclmr.github.ioLanguage: English - Date: 2018-08-06 06:17:49
|
|---|
40 | Add to Reading ListSource URL: www.doc.ic.ac.ukLanguage: English - Date: 2009-08-14 07:09:04
|
|---|