<--- Back to Details
| First Page | Document Content | |
|---|---|---|
 Date: 2008-08-25 02:24:24MD5 MD4 Preimage attack Collision attack Differential cryptanalysis Hash function RIPEMD SHA-2 Merkle–Damgård construction Cryptographic hash functions Cryptography SHA-1 |
Add to Reading List |
 | Improved Differential-Linear Cryptanalysis of 7-round Chaskey with Partitioning Ga¨etan Leurent Inria, France Abstract. In this work we study the security of Chaskey, a recentDocID: 1xTE8 - View Document |
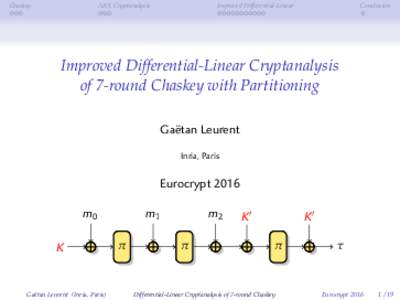 | Chaskey ARX Cryptanalysis Improved Differential-LinearDocID: 1xT7u - View Document |
 | Differential Cryptanalysis of the Data Encryption Standard Eli Biham1 Adi Shamir2DocID: 1udaS - View Document |
 | Precise Fault-Injections using Voltage and Temperature Manipulation for Differential Cryptanalysis Raghavan Kumar$ , Philipp Jovanovice and Ilia Poliane $ University of Massachusetts, 01002 USADocID: 1tfZi - View Document |
 | ¨ Bases) Interactions between Computer Algebra (Grobner and Cryptology `DocID: 1qRIx - View Document |
 Notes on the Wang et al. 263 SHA-1 Differential Path Martin Cochran ∗ August 24, 2008 Abstract Although advances in SHA-1 cryptanalysis have been made since the 2005 announcement of
Notes on the Wang et al. 263 SHA-1 Differential Path Martin Cochran ∗ August 24, 2008 Abstract Although advances in SHA-1 cryptanalysis have been made since the 2005 announcement of