<--- Back to Details
| First Page | Document Content | |
|---|---|---|
 Date: 2005-10-26 13:01:48Keystream Rotor machine Cipher Cryptanalysis One-time pad Block cipher Enigma machine Linear cryptanalysis Differential cryptanalysis Cryptography Stream ciphers Substitution cipher |
Add to Reading List |
 | Improved Differential-Linear Cryptanalysis of 7-round Chaskey with Partitioning Ga¨etan Leurent Inria, France Abstract. In this work we study the security of Chaskey, a recentDocID: 1xTE8 - View Document |
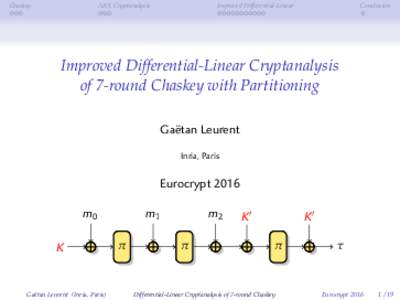 | Chaskey ARX Cryptanalysis Improved Differential-LinearDocID: 1xT7u - View Document |
 | Differential Cryptanalysis of the Data Encryption Standard Eli Biham1 Adi Shamir2DocID: 1udaS - View Document |
 | Precise Fault-Injections using Voltage and Temperature Manipulation for Differential Cryptanalysis Raghavan Kumar$ , Philipp Jovanovice and Ilia Poliane $ University of Massachusetts, 01002 USADocID: 1tfZi - View Document |
 | ¨ Bases) Interactions between Computer Algebra (Grobner and Cryptology `DocID: 1qRIx - View Document |
 Algorithms and Mechanisms Cryptography is nothing more than a mathematical framework for discussing the implications of various paranoid delusions — Don Alvarez
Algorithms and Mechanisms Cryptography is nothing more than a mathematical framework for discussing the implications of various paranoid delusions — Don Alvarez