51 | Add to Reading ListSource URL: ay5ay.w4yserver.atLanguage: German - Date: 2018-04-10 01:50:59
|
|---|
52 | Add to Reading ListSource URL: s3.amazonaws.com- Date: 2017-04-06 17:15:24
|
|---|
53 | Add to Reading ListSource URL: www-kb.is.s.u-tokyo.ac.jpLanguage: English - Date: 2007-08-16 22:48:54
|
|---|
54 | Add to Reading ListSource URL: s3.eurecom.frLanguage: English - Date: 2018-08-14 16:06:29
|
|---|
55 | Add to Reading ListSource URL: copernico.dm.unipi.itLanguage: English - Date: 2009-10-30 12:24:57
|
|---|
56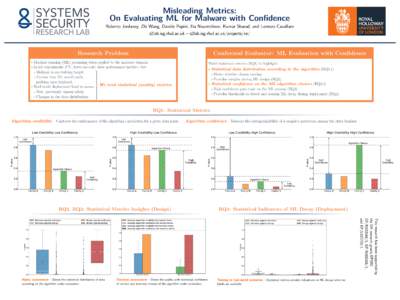 | Add to Reading ListSource URL: ksharad.comLanguage: English - Date: 2018-05-17 15:33:25
|
|---|
57 | Add to Reading ListSource URL: s3.eurecom.frLanguage: English - Date: 2018-08-14 16:06:28
|
|---|
58 | Add to Reading ListSource URL: rpg.ifi.uzh.chLanguage: English - Date: 2014-03-21 05:15:21
|
|---|
59 | Add to Reading ListSource URL: seclab.ccs.neu.eduLanguage: English - Date: 2018-08-14 16:50:48
|
|---|
60 | Add to Reading ListSource URL: s3.eurecom.frLanguage: English - Date: 2018-08-14 16:06:31
|
|---|