<--- Back to Details
| First Page | Document Content | |
|---|---|---|
 Date: 2013-07-02 11:39:49Theft Computer network security Computer security Identity Theft Resource Center Data breach Identity theft International Traffic in Arms Regulations Security Crimes Identity |
Add to Reading List |
 Report Date: Identity Theft Resource Center[removed]Page 1 of 1
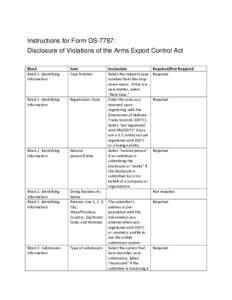
Report Date: Identity Theft Resource Center[removed]Page 1 of 1![Federal Register / Vol. 80, NoFriday, January 16, Rules and Regulations Electronic and Facsimile Availability Supplement No. 2 to Part 748— [Amended] Federal Register / Vol. 80, NoFriday, January 16, Rules and Regulations Electronic and Facsimile Availability Supplement No. 2 to Part 748— [Amended]](https://www.pdfsearch.io/img/4bba7002fb8aa732bf2e2d0ea8780bfe.jpg)