<--- Back to Details
| First Page | Document Content | |
|---|---|---|
 Date: 2017-11-11 14:59:54Cryptography Computational complexity theory Complexity classes Public-key cryptography Interactive proof system NP NEXPTIME IP Probabilistically checkable proof Commitment scheme Proof of secure erasure Randomized algorithm |
Add to Reading List |
 | Randomization, random walks, derandomization, expansion April 12, L´ aszl´ o Babai. Monte Carlo algorithms in graph isomorphism testing.DocID: 1rgOi - View Document |
 | SelectNet_Manual_v2_April_2012.pdfDocID: 1qMoc - View Document |
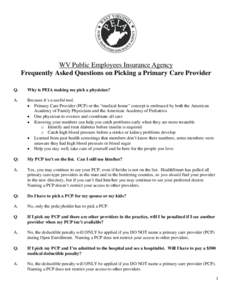 | WV Public Employees Insurance Agency Frequently Asked Questions on Picking a Primary Care Provider Q. Why is PEIA making me pick a physician?DocID: 1qjEP - View Document |
 | Interactive proofs April 12, L´ aszl´ o Babai. Trading group theory for randomness. In Proc. 17th STOC, pages 421–429. ACM Press, 1985. doi:22192.DocID: 1oP1q - View Document |
![Inapproximability of Combinatorial Optimization Problems Luca Trevisan∗ arXiv:cs/0409043v1 [cs.CC] 24 SepJuly 27, 2004 Inapproximability of Combinatorial Optimization Problems Luca Trevisan∗ arXiv:cs/0409043v1 [cs.CC] 24 SepJuly 27, 2004](https://www.pdfsearch.io/img/cd9e8787a29e5952b821e992dbc09a89.jpg) | Inapproximability of Combinatorial Optimization Problems Luca Trevisan∗ arXiv:cs/0409043v1 [cs.CC] 24 SepJuly 27, 2004DocID: 1mroB - View Document |
 Toward practical and unconditional verification of remote computations Srinath Setty∗, Andrew J. Blumberg∗, and Michael Walfish∗ 1 Introduction
Toward practical and unconditional verification of remote computations Srinath Setty∗, Andrew J. Blumberg∗, and Michael Walfish∗ 1 Introduction