<--- Back to Details
| First Page | Document Content | |
|---|---|---|
 Date: 2016-08-24 14:55:21Cryptography Artificial intelligence Human-based computation Computing Cryptocurrencies CAPTCHA Computer security Computer vision Proof-of-work system Hashcash Challengeresponse authentication Zero-knowledge proof |
Add to Reading List |
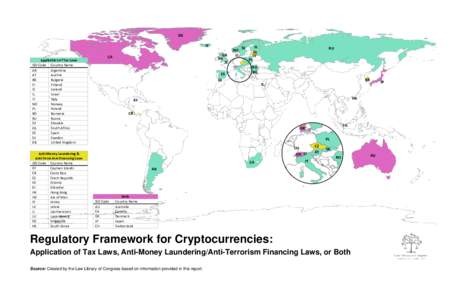 | Regulatory Framework for CryptocurrenciesDocID: 1xVKi - View Document |
 | Hijacking Bitcoin: Routing Attacks on Cryptocurrencies https://btc-hijack.ethz.ch Maria Apostolaki Aviv ZoharDocID: 1xVI1 - View Document |
 | review articles When it comes to anonymizing cryptocurrencies, one size most definitely does not fit all. BY DANIEL GENKIN, DIMITRIOS PAPADOPOULOS, AND CHARALAMPOS PAPAMANTHOUDocID: 1xUXr - View Document |
 | Hijacking Bitcoin: Routing Attacks on Cryptocurrencies https://btc-hijack.ethz.ch Maria Apostolaki Aviv ZoharDocID: 1xUq2 - View Document |
 | Algorand: Scaling Byzantine Agreements for Cryptocurrencies Yossi Gilad, Rotem Hemo, Silvio Micali, Georgios Vlachos, Nickolai Zeldovich MIT CSAIL ABSTRACTDocID: 1xUbv - View Document |
 Designing Proof of Human-work Puzzles for Cryptocurrency and Beyond∗ Jeremiah Blocki Purdue University, Hong-Sheng Zhou Virginia Commonwealth University,
Designing Proof of Human-work Puzzles for Cryptocurrency and Beyond∗ Jeremiah Blocki Purdue University, Hong-Sheng Zhou Virginia Commonwealth University,