<--- Back to Details
| First Page | Document Content | |
|---|---|---|
 Date: 2004-04-30 07:59:55Ciphertext indistinguishability Adaptive chosen-ciphertext attack Malleability Chosen-ciphertext attack Plaintext-aware encryption Advantage RSA Ciphertext Deterministic encryption Cryptography Optimal asymmetric encryption padding Semantic security |
Add to Reading List |
 | Encryption-Scheme Security in the Presence of Key-Dependent Messages J. Black ∗ P. RogawayDocID: 1rlwp - View Document |
 | Certifying RSA Saqib A. Kakvi, Eike Kiltz, and Alexander May Faculty of Mathematics Horst G¨ ortz Institute for IT-Security Ruhr University Bochum, GermanyDocID: 1qO3E - View Document |
 | Practical Cryptanalysis of iso/iecand emv Signatures⋆ Jean-S´ebastien Coron1 , David Naccache2 , Mehdi Tibouchi2 , and Ralf-Philipp Weinmann1 1 Universit´e du Luxembourg 6, rue Richard Coudenhove-Kalergi l-13DocID: 1qNBV - View Document |
 | Randomized Partial Checking Revisited Shahram Khazaei, Douglas Wikstr¨om, February 13, 2012 AbstractDocID: 1qDIf - View Document |
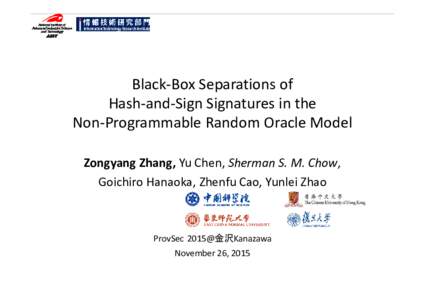 | Microsoft PowerPoint - NPROM-zhang.pptxDocID: 1pGwl - View Document |
 Journal of Cryptology, Volume 17, Number 2. Pages 81–104, Springer-Verlag, 2004.
Journal of Cryptology, Volume 17, Number 2. Pages 81–104, Springer-Verlag, 2004.