121 | Add to Reading ListSource URL: flyer.sis.smu.edu.sgLanguage: English - Date: 2014-12-17 01:40:50
|
|---|
122 | Add to Reading ListSource URL: campuses.fortbendisd.comLanguage: English |
|---|
123 | Add to Reading ListSource URL: www.eecs.umich.eduLanguage: English - Date: 2014-12-24 15:06:41
|
|---|
124 | Add to Reading ListSource URL: cwe.mitre.orgLanguage: English - Date: 2007-07-18 14:25:17
|
|---|
125![=================================================================== PLOVER - Preliminary List Of Vulnerability Examples for Researchers =================================================================== [*] Author: Stev =================================================================== PLOVER - Preliminary List Of Vulnerability Examples for Researchers =================================================================== [*] Author: Stev](https://www.pdfsearch.io/img/f97fb12d0a4060eaa2436dcbae864547.jpg) | Add to Reading ListSource URL: cwe.mitre.orgLanguage: English - Date: 2006-09-13 14:57:16
|
|---|
126 | Add to Reading ListSource URL: www.trailmarathonwales.com- Date: 2015-06-09 06:11:04
|
|---|
127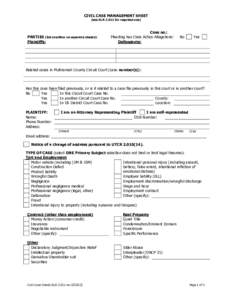 | Add to Reading ListSource URL: courts.oregon.govLanguage: English - Date: 2012-05-15 21:55:30
|
|---|
128 | Add to Reading ListSource URL: assets.selector.comLanguage: English - Date: 2014-05-28 03:26:13
|
|---|
129 | Add to Reading ListSource URL: cwe.mitre.orgLanguage: English - Date: 2007-09-13 16:51:18
|
|---|
130 | Add to Reading ListSource URL: cwe.mitre.orgLanguage: English - Date: 2006-09-13 14:57:15
|
|---|