121 | Add to Reading ListSource URL: www.accaglobal.comLanguage: Russian - Date: 2016-06-13 13:01:43
|
|---|
122 | Add to Reading ListSource URL: www.valdezavalanchecenter.orgLanguage: English - Date: 2016-05-17 18:02:32
|
|---|
123 | Add to Reading ListSource URL: www.parish.gov.jeLanguage: English - Date: 2016-05-26 11:07:41
|
|---|
124 | Add to Reading ListSource URL: www.internetjournalofcriminology.comLanguage: English - Date: 2013-03-29 14:55:57
|
|---|
125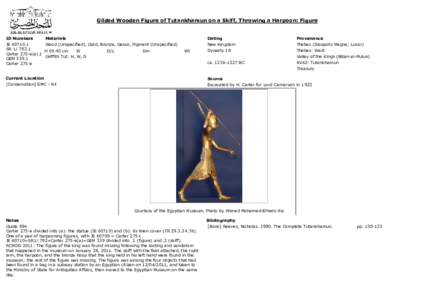 | Add to Reading ListSource URL: www.sca-egypt.orgLanguage: English - Date: 2011-05-05 13:07:49
|
|---|
126 | Add to Reading ListSource URL: capalibrarians.orgLanguage: English |
|---|
127 | Add to Reading ListSource URL: law.adelaide.edu.auLanguage: English - Date: 2014-03-24 00:36:16
|
|---|
128 | Add to Reading ListSource URL: adeona.cs.washington.eduLanguage: English - Date: 2008-09-10 13:43:06
|
|---|
129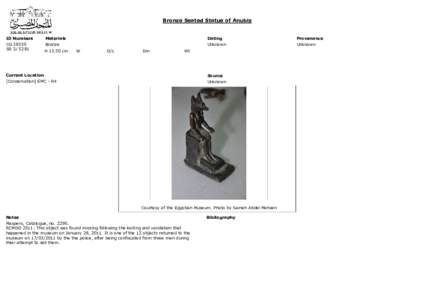 | Add to Reading ListSource URL: www.sca-egypt.orgLanguage: English - Date: 2011-05-05 13:08:36
|
|---|
130 | Add to Reading ListSource URL: miltonkeynes.pm.orgLanguage: English - Date: 2016-02-03 15:58:00
|
|---|