 Date: 2018-06-14 07:12:34Cryptography Data Encryption Standard Linear cryptanalysis Differential cryptanalysis Block cipher Salsa20 Cryptanalysis Differential-linear attack NC Boomerang attack Stream cipher E0 | |  Improved Differential-Linear Cryptanalysis of 7-round Chaskey with Partitioning Ga¨etan Leurent Inria, France Abstract. In this work we study the security of Chaskey, a recent Improved Differential-Linear Cryptanalysis of 7-round Chaskey with Partitioning Ga¨etan Leurent Inria, France Abstract. In this work we study the security of Chaskey, a recent
Add to Reading ListSource URL: who.rocq.inria.frDownload Document from Source Website File Size: 408,73 KBShare Document on Facebook
|


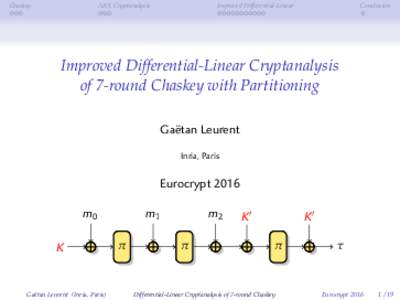


 Improved Differential-Linear Cryptanalysis of 7-round Chaskey with Partitioning Ga¨etan Leurent Inria, France Abstract. In this work we study the security of Chaskey, a recent
Improved Differential-Linear Cryptanalysis of 7-round Chaskey with Partitioning Ga¨etan Leurent Inria, France Abstract. In this work we study the security of Chaskey, a recent