61 | Add to Reading ListSource URL: hm.hgesser.deLanguage: English - Date: 2009-03-04 06:20:29
|
|---|
62 | Add to Reading ListSource URL: css.csail.mit.eduLanguage: English - Date: 2016-01-29 11:50:05
|
|---|
63 | Add to Reading ListSource URL: crd.lbl.govLanguage: English - Date: 2012-09-05 12:41:12
|
|---|
64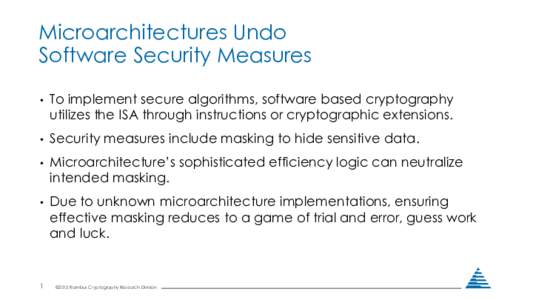 | Add to Reading ListSource URL: www.hotchips.orgLanguage: English - Date: 2015-08-21 02:18:30
|
|---|
65![Layered Assurance Scheme for Multi-Core Architectures J. Alves-Foss, X. He and J. Song Center for Secure and Dependable Systems University of Idaho ,[xhhe,song3202]@vandals.uidaho.edu Layered Assurance Scheme for Multi-Core Architectures J. Alves-Foss, X. He and J. Song Center for Secure and Dependable Systems University of Idaho ,[xhhe,song3202]@vandals.uidaho.edu](https://www.pdfsearch.io/img/63120e9cb1c10a0c3c614895316b6719.jpg) | Add to Reading ListSource URL: fm.csl.sri.comLanguage: English - Date: 2011-12-15 18:21:30
|
|---|
66 | Add to Reading ListSource URL: esec-lab.sogeti.comLanguage: English - Date: 2016-07-01 12:08:46
|
|---|
67 | Add to Reading ListSource URL: hm.hgesser.deLanguage: English - Date: 2009-03-04 06:20:24
|
|---|
68 | Add to Reading ListSource URL: www.cs.columbia.eduLanguage: English - Date: 2016-07-02 09:59:49
|
|---|
69 | Add to Reading ListSource URL: www.ccs.neu.eduLanguage: English - Date: 2014-06-11 17:22:53
|
|---|
70 | Add to Reading ListSource URL: s3-us-west-2.amazonaws.comLanguage: English - Date: 2016-08-01 18:22:08
|
|---|