<--- Back to Details
| First Page | Document Content | |
|---|---|---|
 Date: 2017-10-12 17:24:58Economy Statistical theory Time series models Probability and statistics Machine learning Alternative currencies Cryptocurrencies Digital currencies BoxJenkins method Forecasting Bitcoin Cross-validation |
Add to Reading List |
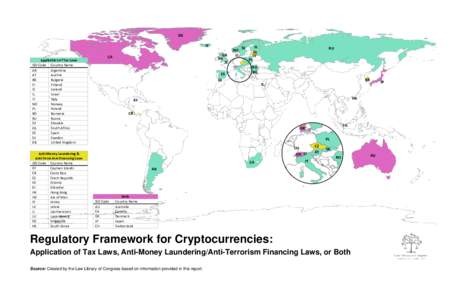 | Regulatory Framework for CryptocurrenciesDocID: 1xVKi - View Document |
 | Hijacking Bitcoin: Routing Attacks on Cryptocurrencies https://btc-hijack.ethz.ch Maria Apostolaki Aviv ZoharDocID: 1xVI1 - View Document |
 | review articles When it comes to anonymizing cryptocurrencies, one size most definitely does not fit all. BY DANIEL GENKIN, DIMITRIOS PAPADOPOULOS, AND CHARALAMPOS PAPAMANTHOUDocID: 1xUXr - View Document |
 | Hijacking Bitcoin: Routing Attacks on Cryptocurrencies https://btc-hijack.ethz.ch Maria Apostolaki Aviv ZoharDocID: 1xUq2 - View Document |
 | Algorand: Scaling Byzantine Agreements for Cryptocurrencies Yossi Gilad, Rotem Hemo, Silvio Micali, Georgios Vlachos, Nickolai Zeldovich MIT CSAIL ABSTRACTDocID: 1xUbv - View Document |
 Trading Bitcoin and Online Time Series Prediction Muhammad J Amjad Operations Research Center
Trading Bitcoin and Online Time Series Prediction Muhammad J Amjad Operations Research Center