1 | Add to Reading ListSource URL: cve.mitre.orgLanguage: English - Date: 2017-08-10 11:48:35
|
|---|
2 | Add to Reading ListSource URL: cve.mitre.orgLanguage: English - Date: 2017-12-27 19:18:59
|
|---|
3 | Add to Reading ListSource URL: cve.mitre.org- Date: 2017-08-10 11:48:35
|
|---|
4 | Add to Reading ListSource URL: www.idirect.net- Date: 2015-03-19 11:37:26
|
|---|
5 | Add to Reading ListSource URL: greenbone.netLanguage: English - Date: 2016-08-19 11:06:48
|
|---|
6 | Add to Reading ListSource URL: resources.sei.cmu.eduLanguage: English - Date: 2015-05-01 17:51:11
|
|---|
7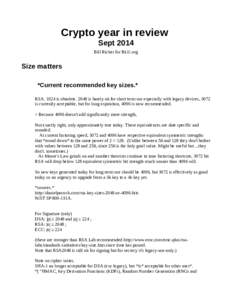 | Add to Reading ListSource URL: blu.orgLanguage: English - Date: 2014-10-02 16:10:38
|
|---|
8 | Add to Reading ListSource URL: home.apache.orgLanguage: English - Date: 2013-02-27 13:13:58
|
|---|
9 | Add to Reading ListSource URL: www.whitehatsec.comLanguage: English - Date: 2016-08-18 19:02:11
|
|---|
10 | Add to Reading ListSource URL: www.interactivenw.comLanguage: English - Date: 2014-10-07 15:06:31
|
|---|