1 | Add to Reading ListSource URL: seclab.illinois.eduLanguage: English |
|---|
2 | Add to Reading ListSource URL: web.engr.illinois.eduLanguage: English - Date: 2015-11-16 12:12:29
|
|---|
3 | Add to Reading ListSource URL: www.profsandhu.comLanguage: English - Date: 2008-02-07 14:26:30
|
|---|
4 | Add to Reading ListSource URL: profsandhu.comLanguage: English - Date: 2008-02-07 14:26:30
|
|---|
5 | Add to Reading ListSource URL: fc12.ifca.aiLanguage: English - Date: 2012-02-18 14:33:45
|
|---|
6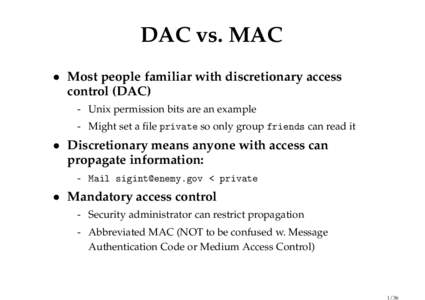 | Add to Reading ListSource URL: www.scs.stanford.eduLanguage: English - Date: 2010-03-04 18:26:58
|
|---|
7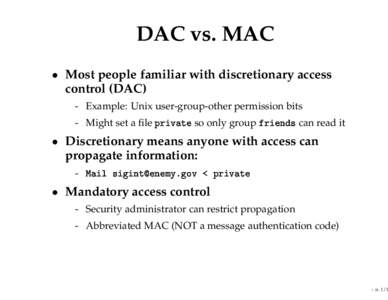 | Add to Reading ListSource URL: www.scs.stanford.eduLanguage: English - Date: 2008-03-06 16:24:21
|
|---|
8 | Add to Reading ListSource URL: www.scs.stanford.eduLanguage: English - Date: 2010-03-04 18:26:58
|
|---|
9 | Add to Reading ListSource URL: swerl.tudelft.nlLanguage: English - Date: 2008-04-25 16:21:05
|
|---|
10![1995 Paper 7 Question 8 Security Explain the difference between discretionary and mandatory access control. [3 marks] Describe the Bell–LaPadula security policy model. 1995 Paper 7 Question 8 Security Explain the difference between discretionary and mandatory access control. [3 marks] Describe the Bell–LaPadula security policy model.](https://www.pdfsearch.io/img/aeaff442f3ddf7f6f3ac1bd7fe2ccd86.jpg) | Add to Reading ListSource URL: www.cl.cam.ac.uk- Date: 2014-06-09 10:17:04
|
|---|