1 | Add to Reading ListSource URL: foresite.comLanguage: English - Date: 2018-02-22 13:10:47
|
|---|
2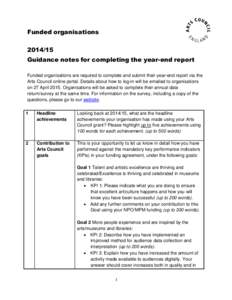 | Add to Reading ListSource URL: www.artscouncil.org.ukLanguage: English - Date: 2015-04-15 12:09:54
|
|---|
3 | Add to Reading ListSource URL: www.computer.orgLanguage: English - Date: 2012-02-29 13:44:30
|
|---|
4 | Add to Reading ListSource URL: www.artscouncil.org.ukLanguage: English - Date: 2014-04-30 07:37:47
|
|---|
5 | Add to Reading ListSource URL: www.blackstratus.comLanguage: English - Date: 2014-04-08 16:03:52
|
|---|
6 | Add to Reading ListSource URL: www.crypttech.comLanguage: English - Date: 2014-09-22 14:14:12
|
|---|
7![Microsoft Word - Data Sheet_LOG Storm_Dec[removed]draft Microsoft Word - Data Sheet_LOG Storm_Dec[removed]draft](https://www.pdfsearch.io/img/74b40feb25301390d48049f4f4e58e01.jpg) | Add to Reading ListSource URL: www.blackstratus.comLanguage: English - Date: 2013-12-20 09:49:56
|
|---|
8 | Add to Reading ListSource URL: www.nict.go.jpLanguage: English - Date: 2005-09-28 07:30:01
|
|---|
9![Building Security In Editors: John Steven, [removed] Gunnar Peterson, [removed] How to Do Application Logging Right Building Security In Editors: John Steven, [removed] Gunnar Peterson, [removed] How to Do Application Logging Right](https://www.pdfsearch.io/img/2cec50ffd73a74b525bcca9ffcde4051.jpg) | Add to Reading ListSource URL: arctecgroup.netLanguage: English - Date: 2010-08-04 12:44:52
|
|---|
10 | Add to Reading ListSource URL: www.state.tn.usLanguage: English - Date: 2013-05-17 11:51:58
|
|---|