1 | Add to Reading ListSource URL: eprint.iacr.org- Date: 2011-01-06 01:53:57
|
|---|
2 | Add to Reading ListSource URL: eprint.iacr.org- Date: 2013-12-09 21:49:28
|
|---|
3 | Add to Reading ListSource URL: www.cs.umd.edu- Date: 2006-12-29 08:35:29
|
|---|
4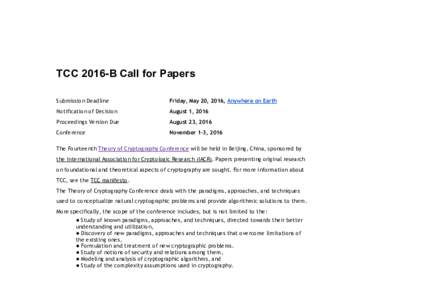 | Add to Reading ListSource URL: tcc2016b.sklois.cnLanguage: English - Date: 2016-05-03 02:55:25
|
|---|
5 | Add to Reading ListSource URL: web.cs.ucdavis.eduLanguage: English - Date: 2003-08-29 18:48:29
|
|---|
6 | Add to Reading ListSource URL: ec14.compute.dtu.dkLanguage: English - Date: 2014-05-16 06:52:20
|
|---|
7 | Add to Reading ListSource URL: eprint.iacr.orgLanguage: English - Date: 2015-01-03 14:06:44
|
|---|
8 | Add to Reading ListSource URL: web.eecs.umich.eduLanguage: English - Date: 2015-09-08 16:32:03
|
|---|
9 | Add to Reading ListSource URL: eprint.iacr.orgLanguage: English - Date: 2011-02-04 14:26:37
|
|---|
10 | Add to Reading ListSource URL: www.cs.tau.ac.ilLanguage: English - Date: 2008-11-05 15:38:44
|
|---|