1 | Add to Reading ListSource URL: www-pdg.lbl.govLanguage: English - Date: 2014-08-21 16:39:14
|
|---|
2 | Add to Reading ListSource URL: pdg.lbl.govLanguage: English - Date: 2014-08-21 16:39:14
|
|---|
3 | Add to Reading ListSource URL: iti.mff.cuni.czLanguage: English - Date: 2016-02-04 05:53:37
|
|---|
4 | Add to Reading ListSource URL: www.sis.uta.fiLanguage: English - Date: 2011-05-10 03:10:48
|
|---|
5 | Add to Reading ListSource URL: hkumath.hku.hkLanguage: English - Date: 2014-11-26 20:00:30
|
|---|
6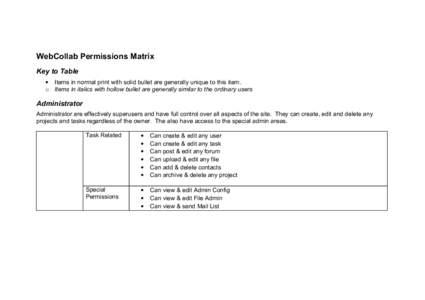 | Add to Reading ListSource URL: webcollab.sourceforge.netLanguage: English - Date: 2010-06-16 23:42:45
|
|---|
7 | Add to Reading ListSource URL: www.numbertheory.orgLanguage: English - Date: 2010-07-04 17:28:46
|
|---|
8 | Add to Reading ListSource URL: eprint.iacr.orgLanguage: English - Date: 2012-12-10 21:50:06
|
|---|
9 | Add to Reading ListSource URL: www.genebee.msu.suLanguage: English - Date: 2001-10-15 03:18:11
|
|---|
10 | Add to Reading ListSource URL: www.numbertheory.orgLanguage: English - Date: 2002-01-31 03:15:38
|
|---|